
Customized AI Adversary Intelligence
Why Broad Threat Reports Falls Short
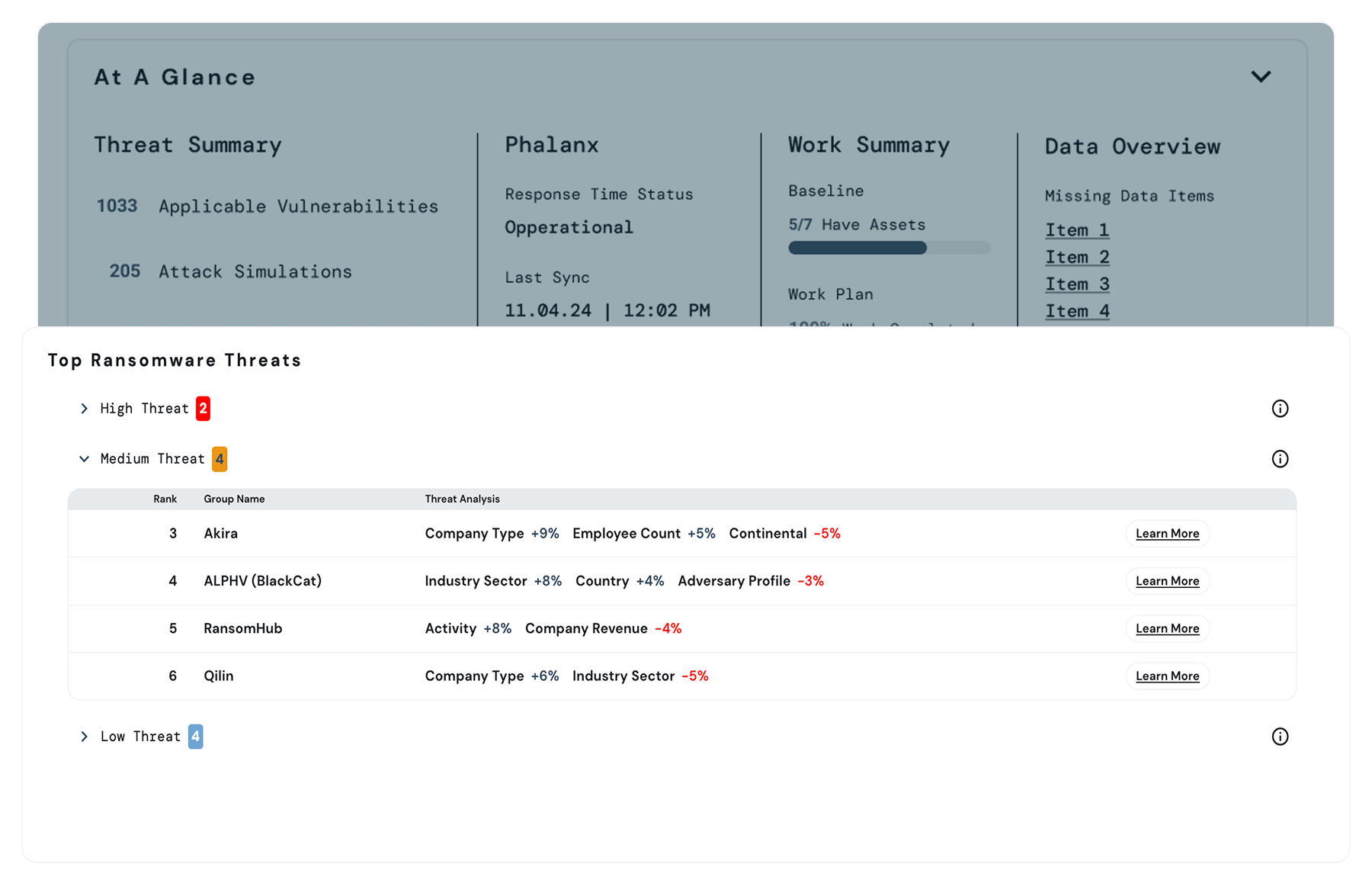
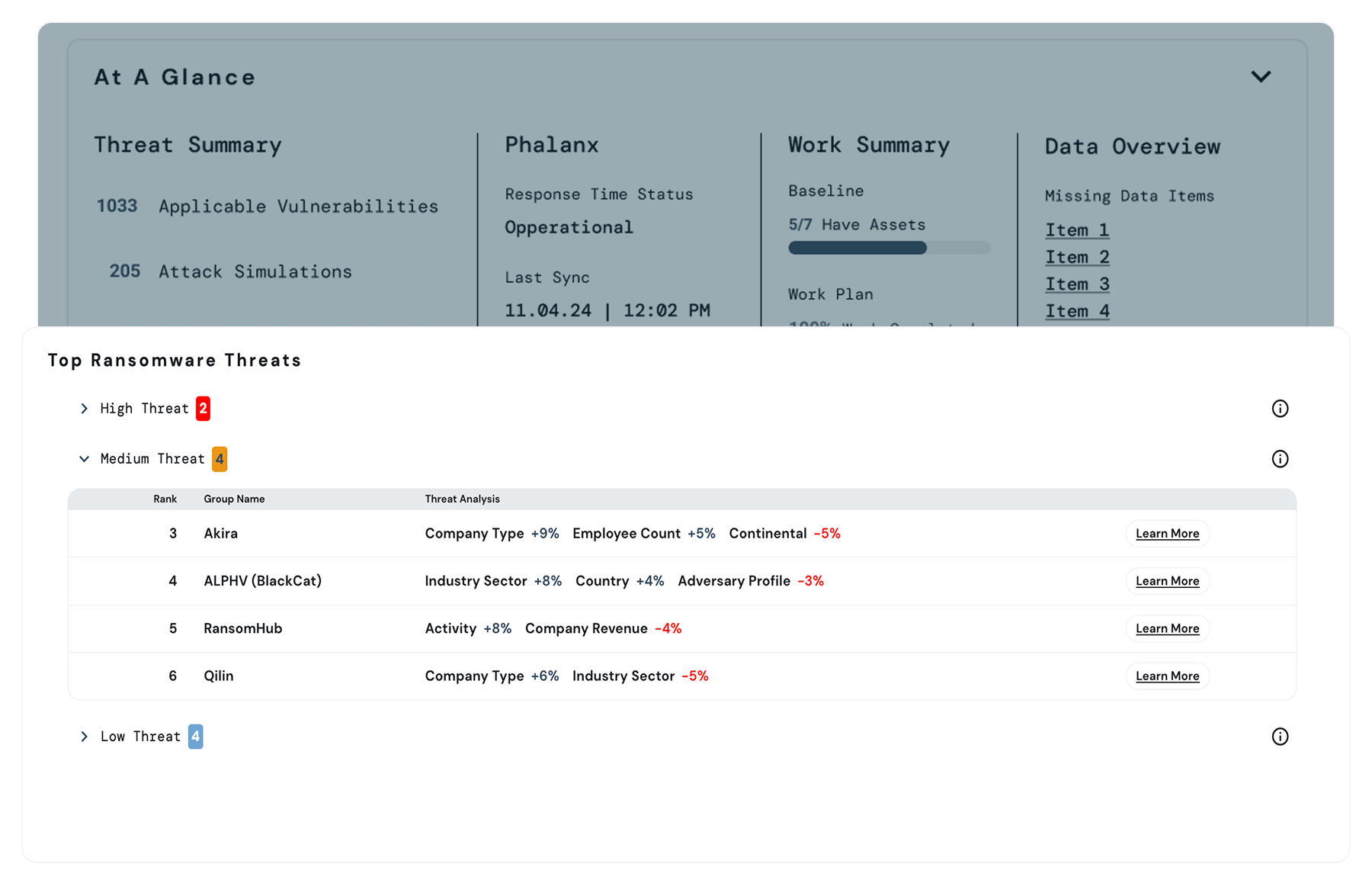
OT teams are flooded with reports on nation-states and ransomware groups but lack clarity on which adversaries are likely to target their environment or how specific tactics align with their vulnerabilities.
These reports contain valuable context about intent and tradecraft that often goes unused. By capturing that deeper meaning with AI-driven modeling, Bastazo turns abstract threat data into actionable insight. It’s one thing to know an adversary uses phishing (T1566); it’s another to understand how they craft campaigns and why, so you can stop the attack before it succeeds.

What Bastazo Adversary Intelligence Does

Built on Research-Backed Threat Modeling
Bastazo’s adversary intelligence is grounded in original research that combines large language models with machine learning to automate the extraction and contextualization of threat actor attributes.
Rather than relying solely on indicators of compromise or static threat lists, Bastazo models adversaries based on who they target, how they operate, and what motivates them, then connects that intelligence directly to organizational risk. This enables more accurate prioritization of defensive actions and security investments.
Manufacturing Firm Defending Against Nation-State Activity
A North American automotive parts manufacturer could use Bastazo’s Adversary Intelligence to identify APT28 as a relevant threat based on its industry, geographic footprint, and OT environment. Bastazo maps APT28’s known tactics and techniques to vulnerabilities in plant-floor and engineering systems, allowing the security team to focus on the most likely paths of exploitation.
Remediation playbooks are updated to limit remote access into OT networks, tighten privileges on engineering workstations, and implement compensating controls on systems that cannot be patched without downtime—reducing exposure to this potential threat activity.