Vulnerability Prioritization Built for OT Reality
Why Vulnerability Prioritization Fails in OT Environments
Effective prioritization requires operational context: how exposed a system is, how critical it is to operations. Traditional severity scoring can capture this reality, but adjusting scores to reflect operational reality is time-consuming. As a result, many fall back on the scores themselves to represent risk, leading to high-severity vulnerabilities with low operational risk taking priority over lower-severity vulnerabilities that pose a real threat.
Bastazo exists to close this gap by aligning vulnerability prioritization with the realities of OT operations in a sustainable and maintainable way for your team.

What Bastazo’s Vulnerability Prioritization Does

How It Works
Ingest vulnerability data
Bastazo ingests vulnerability data from NVD, CISA KEV, and a range of other vulnerability enrichment feeds, then layers in our threat intel data based on your organization’s profile.
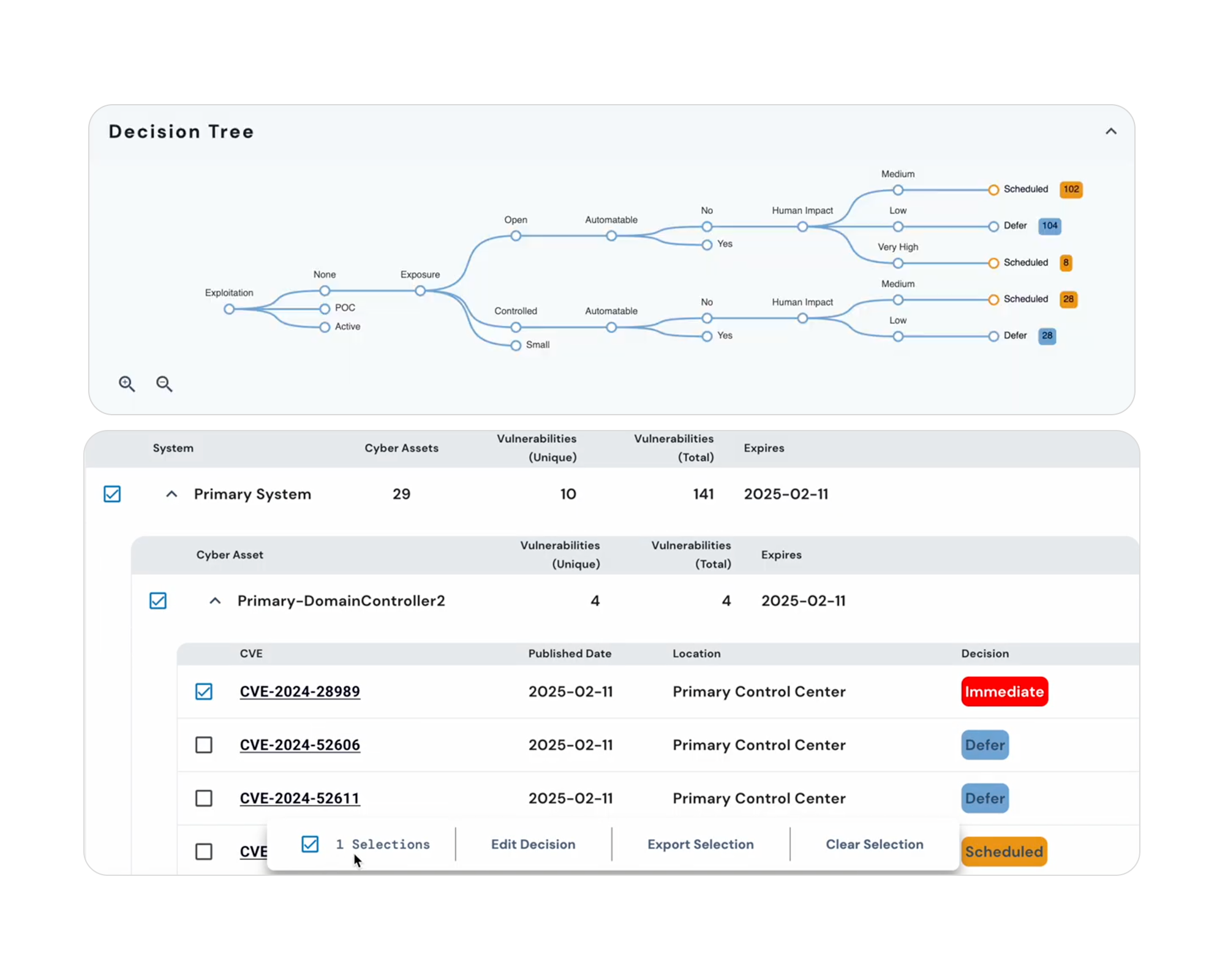
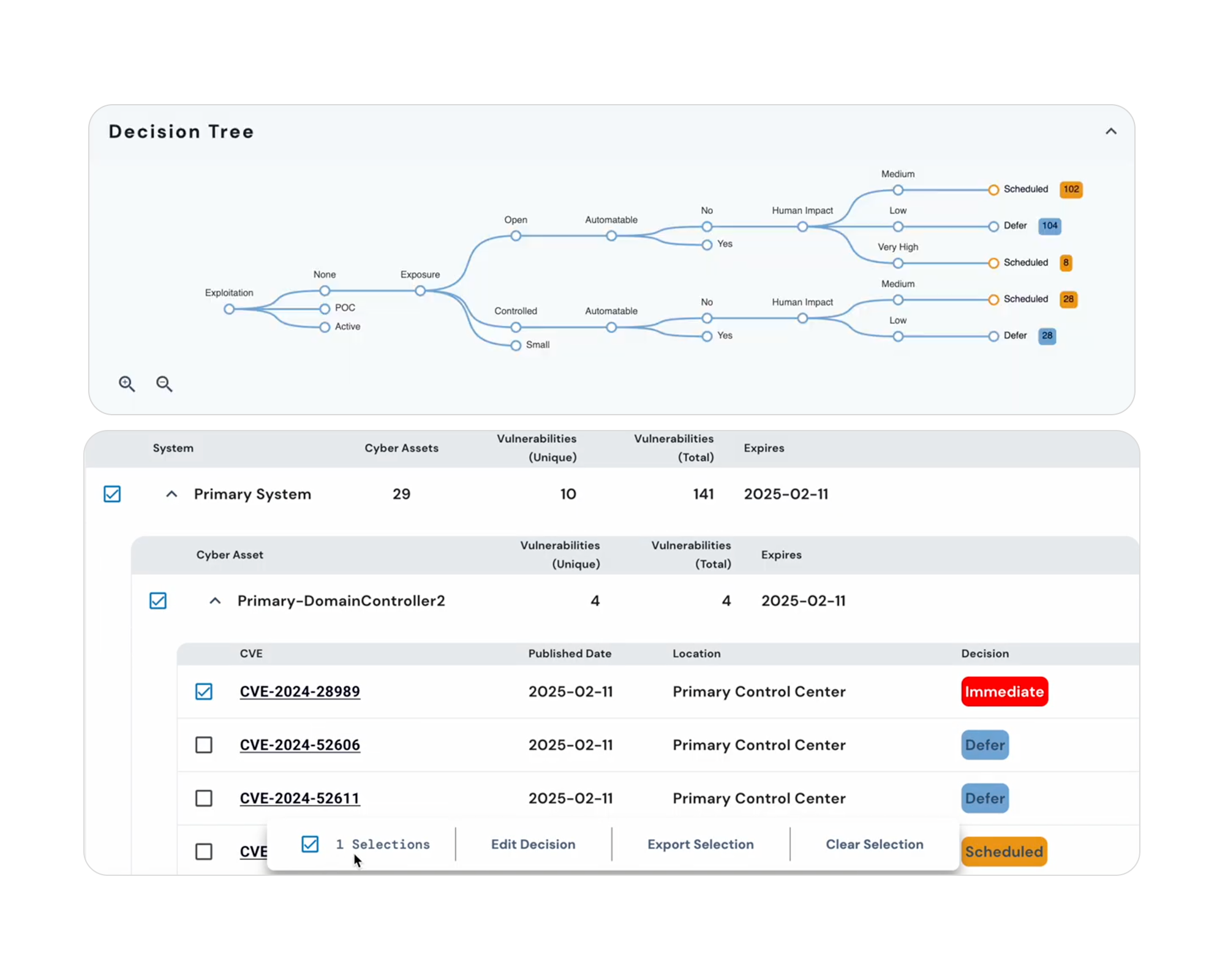
Evaluate real-world risk using SSVC
Each vulnerability is evaluated using SSVC decision criteria, including exploit maturity, system exposure, safety impact, and operational consequences.
Decide what action is required
Instead of producing a numeric risk score, Bastazo classifies vulnerabilities into clear, actionable categories that answer one operational question: What should we do next?
Focus on what truly matters
The result is a prioritized set of vulnerabilities (typically the most critical ~5%) that represent the greatest risk to your organization.
Ongoing Vulnerability Monitoring
Bastazo’s software continuously monitors for changes in existing vulnerabilities, too. This means that if a vulnerability becomes exploited, you will be notified and can re-evaluate the vulnerability priority with this new information.
Key Outcomes for OT teams
Clear prioritization without debate or guesswork
Reduced time to remediation on highest risk vulnerabilities
Transparent documentation for audits and compliance
Why Bastazo Is Different
FAQs
SSVC requires three fields for operational context: Exposure, Safety Impact, and Mission Impact; these are required for each asset. In some cases, Bastazo is able to infer these values and then allow the user to validate or change them. Most importantly, these values are largely static and do not often change during a device’s lifecycle, allowing you to spend time fixing critical issues instead of updating these fields.













